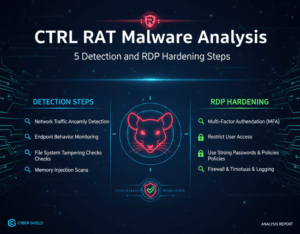
CTRL RAT Malware Analysis: 5 Detection and RDP Hardening Steps
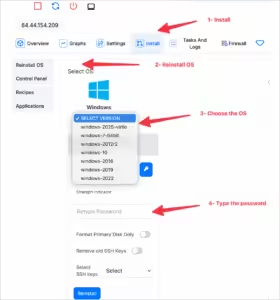
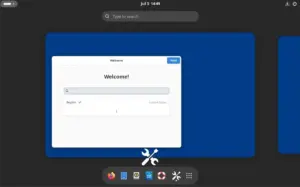
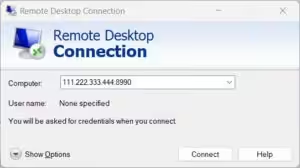
The emergence of the CTRL toolkit has introduced a sophisticated, fileless post-exploitation framework that operators are utilizing to gain stealthy, hands-on access to Windows systems. By integrating credential